From Registered Investment Advisors (RIAs) and Family Offices to Credit Unions and Community Banks, it’s important to have a well-defined technology vendor due diligence process in place to meet compliance and ensure you are investing your dollars where they count.
As demand within the financial services and wealth management industry increases and client expectations continue to evolve, C-level executives and advisors have turned to third-party service providers to handle certain functions or services, some of which are required for advisors to comply with regulations when providing their services.
The Securities and Exchange Commission (SEC) recently proposed a new rule and rule amendments under the Investment Advisers Act of 1940 to prohibit registered investment advisers (RIAs) from outsourcing certain services and functions without conducting due diligence and monitoring of the service providers.
The recent updates to regulations require advisors to meet certain due diligence requirements before hiring a service provider to perform certain advisory services or functions. Advisors must also regularly monitor the performance of the service provider. This rule applies to advisors who outsource certain “covered functions,” which are services or functions that are necessary for the advisor to comply with Federal securities laws and that, if not performed or performed improperly, could significantly harm clients.
These functions may include investment guidelines, portfolio management, investment advice-related models, indexes, trading services, and of course, technology and software. While outsourcing can be beneficial for firms, advisors, and their clients, it can also cause harm to clients if the advisor outsources a function or service without proper oversight.
Below are several reasons why having a well-defined and structured vendor due diligence process (or checklist) for the technology providers — and other third-party providers — that you work with is incredibly important for your firm in 2023.
- To ensure compliance: Firms and institutions have a responsibility to comply with regulations, and using technology vendors that do not meet regulatory requirements can expose the firm or institution to legal and financial risks.
- To protect client/household data: Firms and institutions handle sensitive client information and data, and it is important to ensure that third-party technology vendors have sufficient information security measures in place to protect this data.
- To protect the firm’s reputation: Using technology vendors that do not meet industry standards or that have a history of security breaches can damage the firm’s reputation.
- To protect the firm’s financial interests: Using unreliable or insecure technology can lead to costly disruptions and downtime, which can negatively impact the firm’s financial performance.
- To ensure vendor stability: Conducting due diligence on third-party technology vendors can help the firm or institution assess the vendor’s financial stability and long-term viability. This is important because the firm or institution will be relying on the vendor to provide ongoing support and maintenance for their products or services.
What is vendor due diligence?
Vendor due diligence (VDD) is a comprehensive platform, features, and security screening of a potential third-party vendor, including technology vendors, before forming a partnership or committing to a contractual obligation. The assessment identifies whether a prospective vendor can meet and exceed the expectations of your firm’s requirements and ensure that there is a process in place to address any and all potential concerns and risks associated with a potential partnership or relationship.
A Guide to Evaluating Third-Party Vendors
There is no questioning that in recent years technology has become a deeply embedded and fundamental part of financial services and wealth management firms. It’s no longer just a nice-to-have, but an essential component of any firm’s overall value offering and its day-to-day operations.
To say the least, technology and modern financial services go hand-in-hand.
However, ensuring that your firm partners with the right technology provider is a different story; one that can either provide your firm with a massive advantage or disadvantage.
Here are some fundamental questions and steps you should consider when assessing a potential relationship with a third-party technology service provider:
1) Data Protection and Security
One of the most critical areas of assessment when undergoing the due diligence process with a third-party vendor is Data Protection and Data Security. Any technology vendors, including your digital vault platform and document management solution, that will be in possession of enterprise and clients’ personally identifiable information should prove the steps they take to ensure the safety of such data.
The easiest and most effective way to ask for this proof is to request a SOC 2 Report. This is incredibly important to showcase and demonstrate to clients and regulators that you take the security of client data seriously and you have examined all vendors’ processes and procedures related to data security.
Remember, your firm can have the tightest cybersecurity measures in place, but you are only as strong as your weakest link – it’s always in your best interest to confirm that the technology provider you select is one that becomes a trusted partner; by your firm, by your clients, and by regulators.
Here at FutureVault, we proudly provide a copy of our SOC 2 Type II Report to the firms that we work with (with our most recent report being issued by Ernst & Young in September 2022). If any vendor you are deciding to work with refuses to provide a copy of its SOC 2 report or takes their time in providing you with this proof, that is a 🚩massive red flag 🚩 and likely means that you’re better off running for the hills.
2) Information and Data Ownership
To ensure smooth transitions and avoid potential problems in the future, it is important to get a clear understanding of the ownership and transferability of client data on a technology vendor’s platform before signing a contract with them. Specifically, you should confirm whether or not you will be able to take your data with you if the contract expires. If the process for transferring data from and to another vendor is unclear or difficult, you may want to consider alternative solutions.
3) Organization Size and Depth
For small RIAs with 10-20 team members, outsourcing key functions can be a useful way to manage “key man risk”, where the departure of an important employee could disrupt the business. However, this strategy is only effective if the vendor has a team of skilled professionals who are familiar with your firm and can support your business on an ongoing basis. If you are relying on a single contractor, you are not fully mitigating key man risk. It is important to consider the size and stability of the vendor’s service team to ensure that they will be able to support your needs for the duration of your partnership.
4) Contract (Re)Assignability
When evaluating potential vendors, it is important for RIAs to consider the assignability of the contract in the event of a merger or acquisition. In the event that your RIA is acquired by a larger organization, you will want to ensure that there is a clear process in place for transferring the vendor contract to the new owner. This will help to ensure a smooth transition and prevent any disruption of service. It is advisable to clarify this process early in negotiations with the vendor to avoid any issues in the future.
5) Pricing Mechanics
When choosing a technology vendor, it is important to understand the various pricing options and methods that are available. These may include pricing based on assets on the vendor’s platform, assets under administration or management by the firm or institution, number of accounts, number of users/licenses, and contract length. It is advisable to clarify any questions about pricing during negotiations, such as whether a longer contract will result in a discounted rate. Understanding how your firm can reach different price breakpoints will help you make informed decisions about the vendor and pricing structure that best fits your needs.
6) Integrations with Other Technology and APIs
In the wealth management and financial services industry, it is essential for technology vendors to offer seamless integrations with other systems. When a vendor claims that their system can integrate with your existing technology stack and other third-party solutions, it is important to understand exactly what this means.
Is data able to flow smoothly between systems in both directions, or are there limitations on the flow of data? Before signing a contract with a vendor, it is crucial to consider the importance of integration with other components of your front and back office and to clarify any questions about integration to ensure that the vendor’s system meets your needs.
An incredibly important factor when assessing the integration capabilities of any technology vendor is to consider the reliability of their APIs (Application Programming Interfaces). APIs allow different systems to communicate and exchange data with each other, and it is important to ensure that the vendor’s APIs are trusted and reliable. Inadequately designed or maintained APIs can lead to errors and disruptions in service, which can have serious consequences for your business.
Note: This is not a comprehensive list of due diligence questions for vendor discussions and should be considered as a starting point to help your firm better understand the types of questions and areas you need to consider. To ensure compliance with the latest requirements, it is recommended that RIAs consult with their compliance officers/consultants and/or an attorney.
Third-Party Vendor Due Diligence Recordkeeping
Under the new rules and amendments, firms are required to maintain accurate and thorough records of their due diligence process for third-party vendors. A secure, cloud-based digital document vault is essential for storing and archiving vendor records, including SOC 2 reports amongst other critical types of documentation.
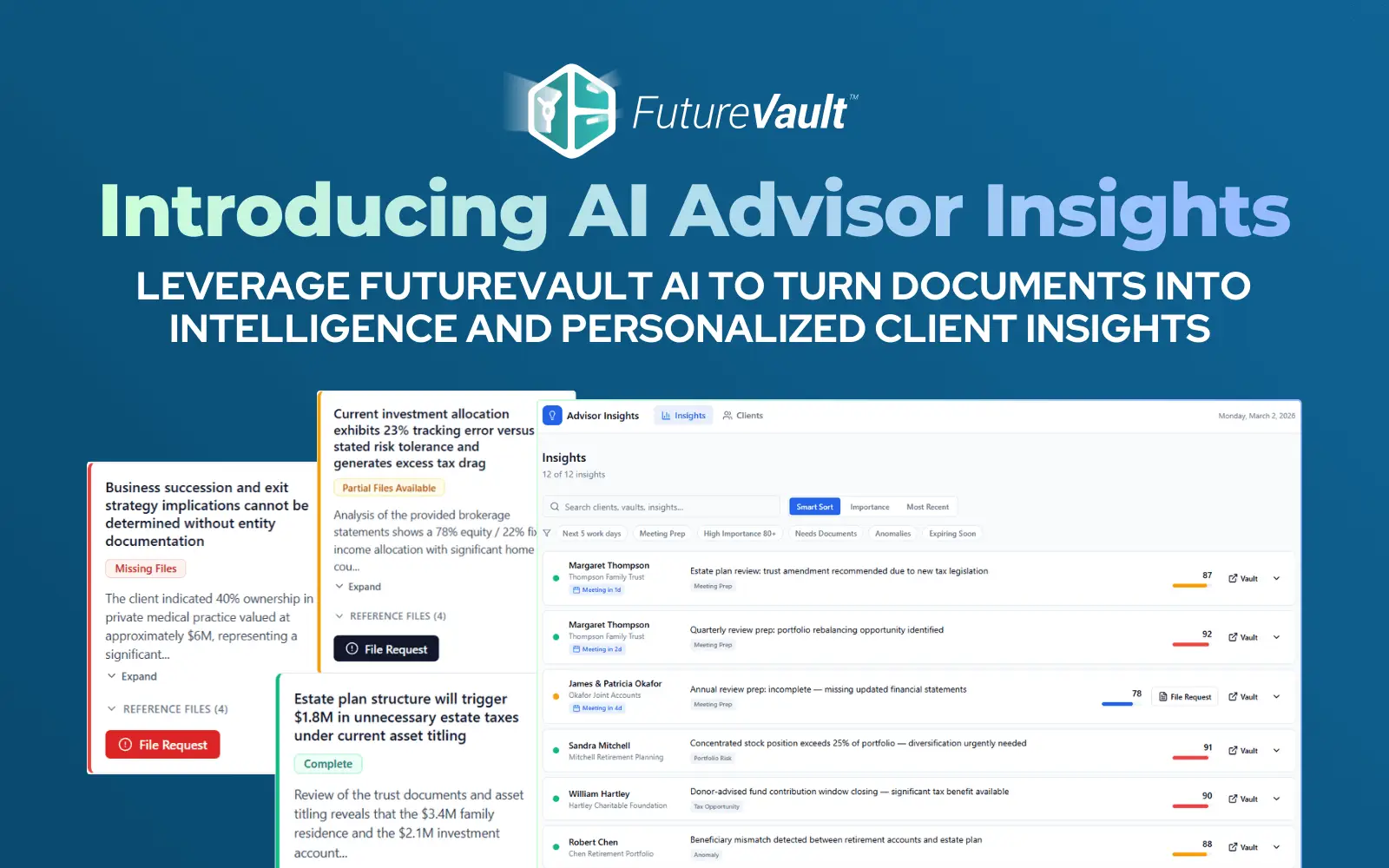
FutureVault’s compliance/corporate Vault allows firms to store and protect sensitive enterprise and compliance-related documentation in a tamper-proof format (WORM), satisfying document retention requirements (including Rule 17a-4) and streamlining external, on-demand audits by regulators.
We recommend that our partners/customers store a copy of our recent report in their Corporate Vault to ensure compliance and have it readily available for regulatory bodies such as FINRA, SEC, and IIROC, amongst other regulatory agencies.
Having a single, secure source of truth for all enterprise, back office, front office, and client documents can provide your firm with confidence, assurance, efficiency, and peace of mind.
As we always say, what happens in the Vault, stays in the Vault.
You deserve peace of mind knowing that your enterprise and client documents are kept safe and secure, at all times.